signal & domain
Introducing data safely into autonomous systems
Waxell Signal and Domain is a governed data boundary layer for autonomous AI agent systems — Signal defines how external systems send information into the Waxell runtime, and Domain defines how agents request actions from external systems, with every input and output logged and policy-enforced.
Autonomous systems are only as reliable as the data they can access.
Most architectures force a trade-off between usefulness and control. Agents either run in isolation with incomplete context or are granted direct access to production systems, creating security and traceability risk.
Waxell introduces Signal and Domain to resolve this trade-off. Together, they define how data enters and leaves agent systems in a controlled, inspectable way.
Free during beta.

Most agent frameworks assume that agents can read from and write to production systems directly.
This creates two structural problems. It requires exposing internal systems or deploying application stacks into the agent runtime, and it breaks traceability by scattering execution data across systems the platform cannot observe.
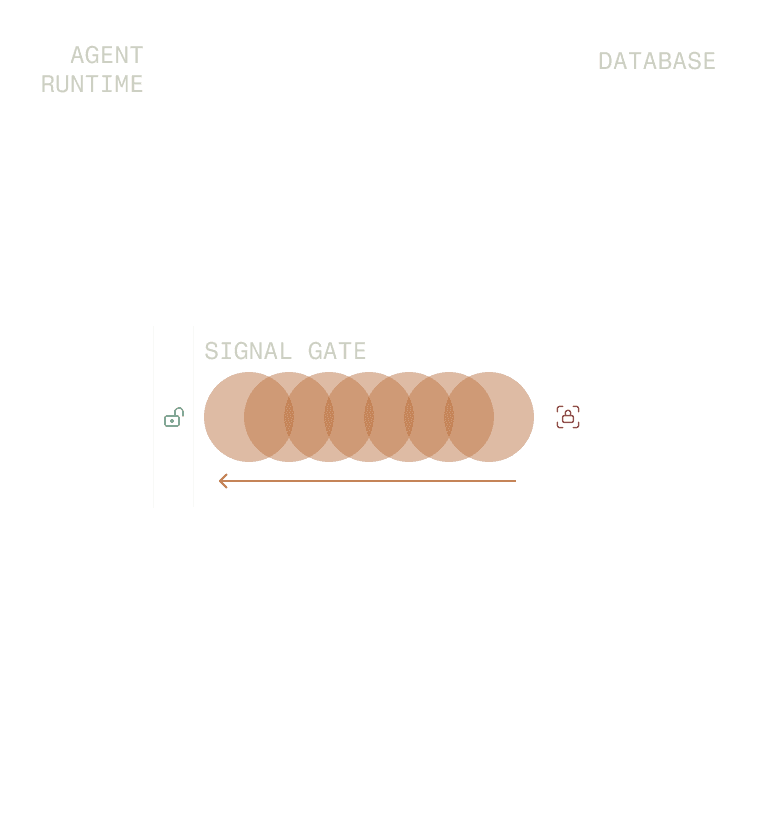
Signal and Domain prevent both outcomes. They create a narrow, governed communication surface instead of broad, implicit access.
Signal: bringing data into the runtime
Signal defines how external systems send information into Waxell.
It allows a company's application or backend to notify agents about events, state changes, or new data without granting direct database access. Every Signal invocation is logged as part of the agent's execution context.
This creates a durable record of what information entered the system, when it arrived, and how it influenced downstream behavior.
Separation of concerns by design
Signal and Domain create a clean boundary between agent execution and production systems.
Agents never access production databases directly. External systems never run inside the Waxell runtime. Communication occurs only through well-defined, secured interfaces.
This separation allows teams to introduce autonomous systems without re-architecting their application stack or weakening existing security controls.

With Signal and Domain in place, all data entering and leaving an agent becomes observable.
Every Signal input and every Domain action is recorded as part of the agent's execution history. Signal and Domain close the traceability gap that opens when agents operate partly outside the platform's visibility.
Teams can inspect not only what an agent decided, but also what information it received and what actions it attempted across the full workflow.
How does Waxell govern AI agent data access?
Signal and Domain integrate directly with Waxell's governance plane.
Policies and kill-switches can be applied at the Domain level to block categories of actions or halt execution when unsafe behavior is detected. Permissions can be scoped narrowly to limit what agents are allowed to request.
This makes data access and action execution first-class governance surfaces rather than hidden side effects.

Incremental adoption, no infrastructure overhaul
Signal and Domain don't require changes to existing production systems. Teams can introduce agent capabilities incrementally — connecting one system to Signal, defining one Domain endpoint — without migrating infrastructure or weakening existing security controls.
The communication boundary is defined at the Waxell level. Production stays intact.
POLICY A
POLICY B
POLICY C
POLICY D
Designed to scale